With quantum breakthroughs threatening RSA encryption, organizations must pivot to a secure self-hosted AI infrastructure to protect sensitive data and IP.
The Quantum Threat: Preparing a Secure Self-Hosted AI Infrastructure for Post-RSA Encryption
In early March 2026, the cybersecurity landscape experienced a seismic shift that effectively collapsed the timeline for post-quantum cryptography (PQC) migration. The global assumption that standard RSA and Elliptic Curve Cryptography (ECC) would remain secure for another decade was shattered by the simultaneous publication of two major quantum computing breakthroughs: the JVG algorithm and the Pinnacle Architecture. These advancements have drastically lowered the qubit threshold required to break the mathematical foundations of modern digital trust. For technology leaders, this "quantum apocalypse" means that sensitive data encrypted today is already vulnerable to interception. To protect proprietary large language models (LLMs), training datasets, and enterprise secrets from imminent decryption, organizations must urgently rethink their data protection strategies. The most viable defense mechanism moving forward is the deployment of a secure self-hosted ai infrastructure that integrates newly finalized post-quantum cryptography standards, ensuring sensitive AI workloads remain sovereign, localized, and mathematically shielded from next-generation quantum attacks.
The March 2026 Breakthroughs: A Timeline Collapsed
For years, the cybersecurity industry operated under a comforting assumption: breaking 2048-bit RSA encryption would require Shor’s algorithm running on theoretical machines boasting millions of physical qubits. As of March 2026, that assumption is dangerously obsolete.
Two distinct research milestones have fundamentally altered the threat matrix:
The JVG Algorithm
On March 2, 2026, the Advanced Quantum Technologies Institute (AQTI) announced the Jesse-Victor-Gharabaghi (JVG) algorithm. This hybrid approach offloads significantly more of the computational workload to classical systems, reducing the required quantum gate count by more than 99% compared to traditional approaches.
According to researchers, the JVG algorithm requires approximately 1,000 times fewer quantum resources than previous best-known methods. Research projections indicate it could break RSA and ECC encryption using fewer than 5,000 logical qubits, factoring RSA-2048 with a projected quantum runtime of just 11 hours blogs.groupware.org.uk.
Iceberg Quantum's Pinnacle Architecture
In the same week, Sydney-based startup Iceberg Quantum published details of their Pinnacle Architecture. Utilizing Quantum Low-Density Parity Check (qLDPC), this architecture drops the physical qubit requirement for breaking RSA-2048 to under 100,000.
"In 2019, the consensus estimate for breaking RSA-2048 on a quantum computer stood at 20 million physical qubits. By May 2025, Craig Gidney had collapsed that to under one million. Now, in February 2026... the number is under 100,000." — postquantum.com
While achieving these numbers requires overcoming immense engineering constraints—such as non-local connectivity and real-time qLDPC decoding—the trajectory is undeniable. The hardware requirements for cryptanalysis are shrinking exponentially.
The "Harvest Now, Decrypt Later" Threat to Enterprise AI
The immediate danger to enterprises is not that a quantum computer will hack their live databases tomorrow, but rather a strategy known as Harvest Now, Decrypt Later (HNDL).
State-sponsored actors and sophisticated criminal organizations are currently intercepting and storing encrypted data at scale. Every secure API call made to a third-party cloud AI provider, every fine-tuning dataset transmitted over standard TLS, and every proprietary prompt containing corporate secrets is being archived.
For AI practitioners, this is a critical vulnerability. AI models are trained on an organization's most valuable intellectual property. If a company relies on cloud-based AI services, their data must transit the public internet. If intercepted today, attackers simply wait until quantum hardware matures—which AQTI and Iceberg Quantum have proven is happening faster than anticipated—to decrypt the stored traffic medium.com.
Despite this existential threat to data privacy, enterprise readiness is alarmingly low. A recent survey by Keyfactor revealed that 48% of technology and security leaders remain completely unaware of quantum migration budgets within their organizations aicerts.ai.
Architecting a Secure Self-Hosted AI Infrastructure
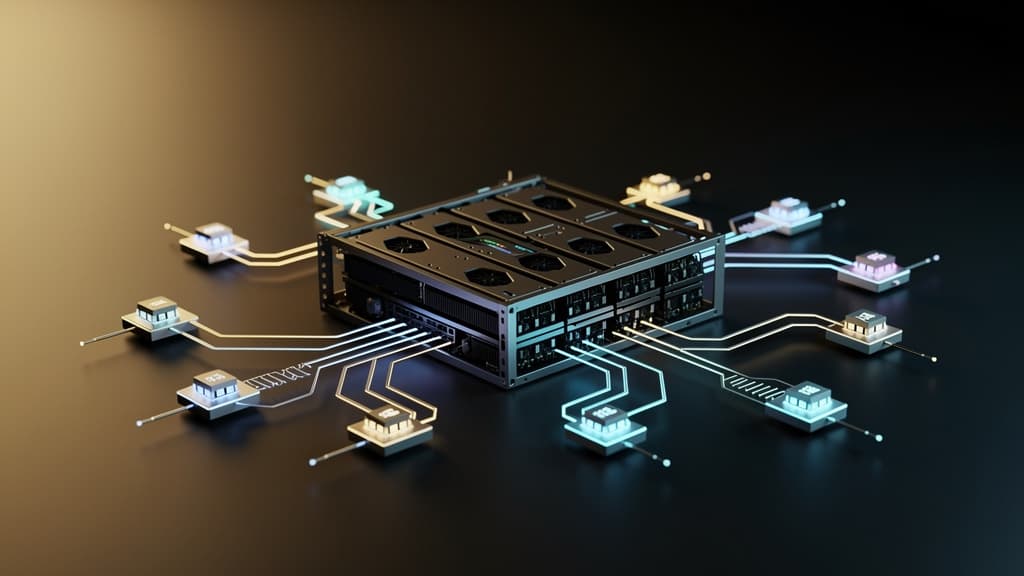
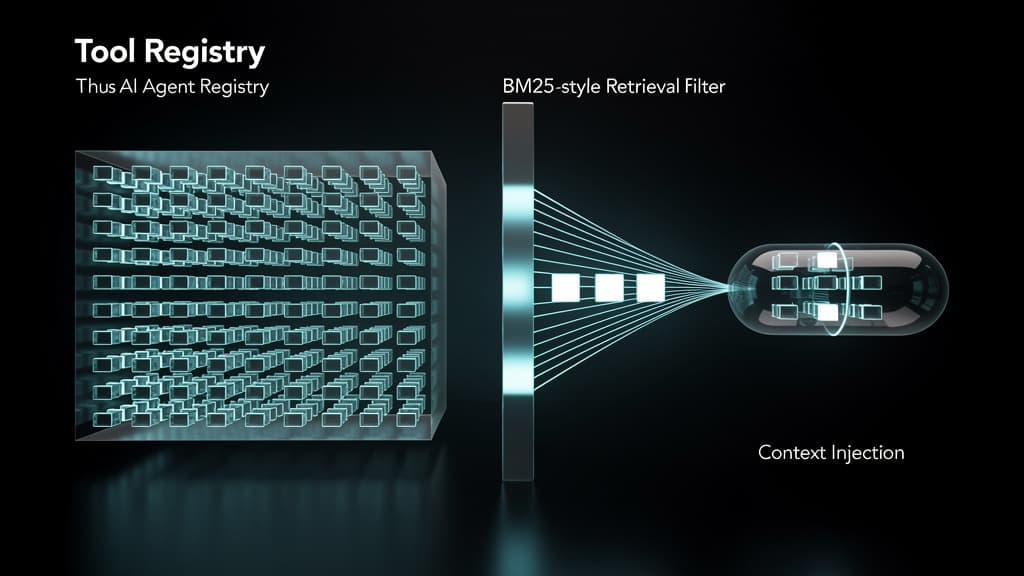
To mitigate the HNDL threat, technology decision-makers must eliminate vulnerable network transit for their most sensitive AI workloads. The strategic imperative is to build a secure self-hosted AI infrastructure. By bringing model inference, Retrieval-Augmented Generation (RAG) pipelines, and fine-tuning entirely in-house, organizations can drastically reduce their cryptographic attack surface.
Here is how enterprises can fortify their internal AI infrastructure for the post-quantum era:
1. Implement NIST's 2024 Post-Quantum Standards
In 2024, the National Institute of Standards and Technology (NIST) released its final post-quantum cryptographic standards (such as ML-KEM for key encapsulation and ML-DSA for digital signatures). While federal agencies are planning RSA deprecation between 2029 and 2035, the March 2026 breakthroughs dictate that private enterprises must accelerate this timeline aicerts.ai. Internal traffic between self-hosted AI servers, vector databases, and application frontends must be upgraded to these quantum-resistant algorithms immediately.
2. Localize Inference and Air-Gap Sensitive Workloads
A secure self-hosted AI infrastructure allows organizations to run open-weight models (like Llama 3 or Mistral) on sovereign hardware. For highly classified workloads—such as financial forecasting models or healthcare diagnostics—these local clusters can be entirely air-gapped. If data never traverses an external network, it cannot be harvested by adversaries waiting for quantum decryption capabilities.
3. Transition to Hybrid Cryptography for External Access
Where external access to the self-hosted infrastructure is unavoidable (e.g., remote employees querying an internal AI assistant), organizations must deploy hybrid cryptographic tunnels. This involves wrapping traditional encryption (like TLS 1.3 with ECC) inside a post-quantum algorithm layer. Even if the traditional encryption is eventually broken by a quantum computer, the PQC layer will protect the intercepted data.
The Cost of Inaction
The convergence of AI and quantum computing represents the most significant security paradigm shift since the invention of public-key cryptography. The algorithms required to break our current security models already exist, and the hardware is scaling rapidly to meet them.
Organizations that continue to route their proprietary AI workflows through standard RSA-encrypted cloud pipelines are effectively handing their future intellectual property to adversaries. Building a secure self-hosted AI infrastructure is no longer just a matter of regulatory compliance or latency optimization—it is a fundamental requirement for corporate survival in the post-quantum era.
Frequently Asked Questions
Q: What is the JVG algorithm and why does it accelerate the quantum threat?
The Jesse-Victor-Gharabaghi (JVG) algorithm is a newly published quantum decryption method that requires roughly 1,000 times fewer quantum resources than Shor's algorithm. By offloading more work to classical computing systems, it reduces the quantum gate count by over 99%, potentially allowing threat actors to break RSA-2048 encryption with fewer than 5,000 logical qubits in just 11 hours.
Q: How does "Harvest Now, Decrypt Later" (HNDL) affect AI models?
HNDL is a strategy where attackers intercept and store encrypted network traffic today, intending to decrypt it once quantum computers are powerful enough. If you send proprietary training data, sensitive prompts, or model weights to cloud AI providers using standard encryption, that data can be harvested. Once decrypted in the future, your organization's core intellectual property and AI strategies will be fully exposed.
Q: Why is a secure self-hosted AI infrastructure critical for post-quantum defense?
Self-hosting your AI models and infrastructure minimizes or entirely eliminates the need to transmit sensitive data across the public internet. By keeping inference, fine-tuning, and vector databases on local, sovereign hardware—and securing internal communications with NIST's 2024 post-quantum standards—you remove the opportunity for adversaries to harvest your encrypted data in transit.
Last reviewed: April 01, 2026